Microsoft Office 365 connector
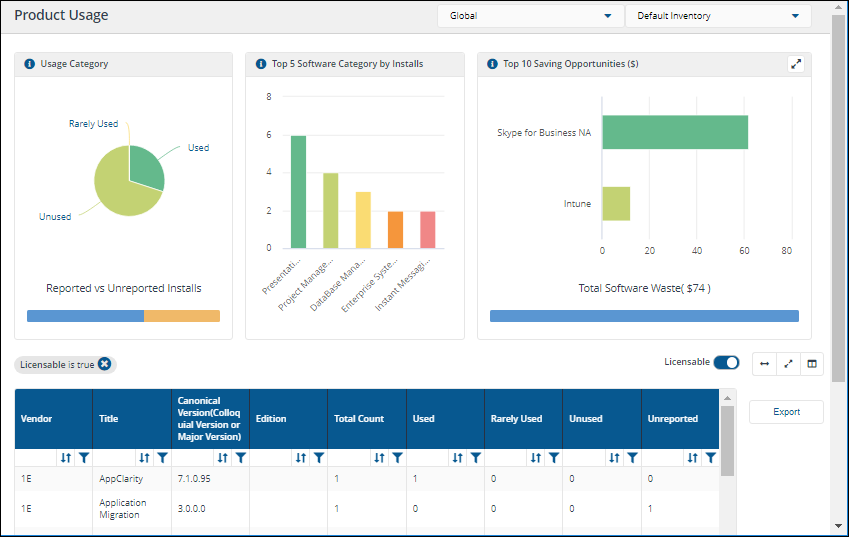
The Microsoft Office 365 connector connects to an Office 365 application in InTune and pulls inventory and usage data.
The configuration procedure described below assumes that you have an InTune and Microsoft Office 365 subscription and can populate the connector with details from an Enterprise Application in your Microsoft Entra ID Console.
Prerequisites
Before adding this connector, you will need the following information from an Enterprise Application created in your AAD console:
-
An Azure cloud instance URL (optional). If this is not supplied, then AzurePublic is used as a default.
-
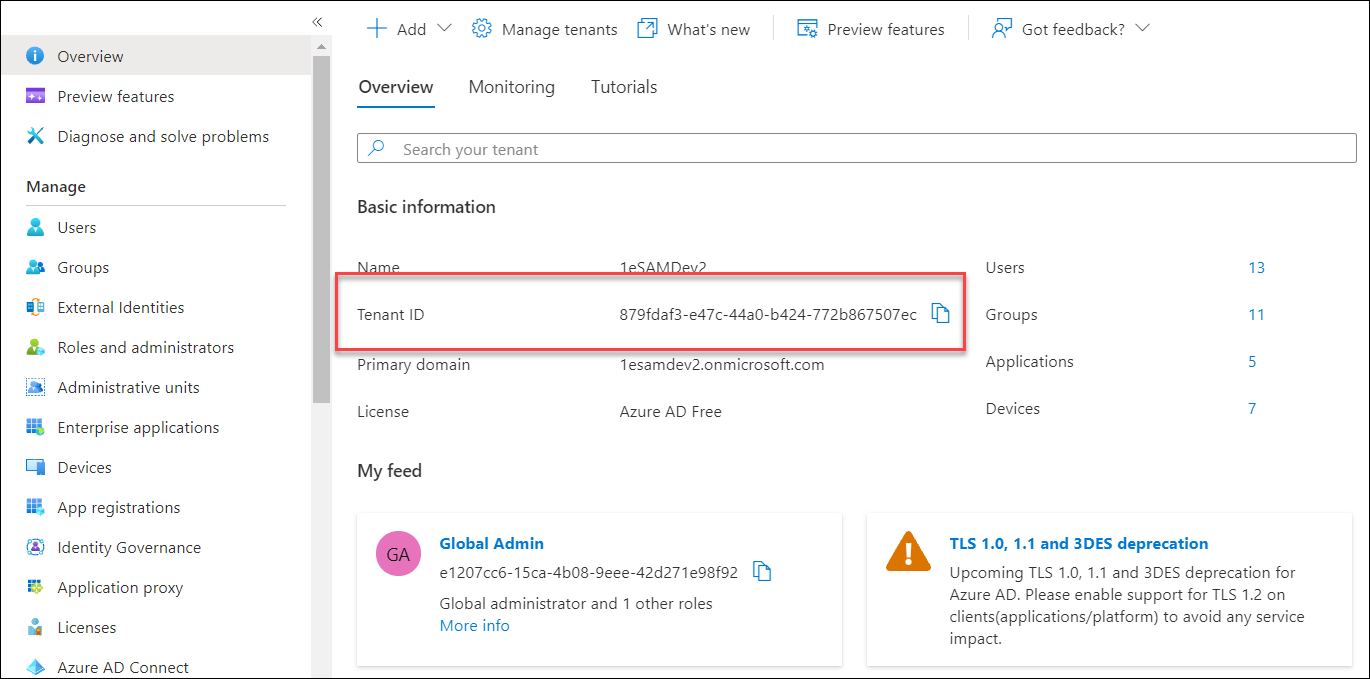
An Azure Tenant ID, which is available in the Overview node of your AAD console.
-
The registered application clientID (a string representing a GUID).
-
A client secret value that has been created for your chosen Enterprise Application.
-
Single sign-on-enabled service account with global reader permissions for running PowerShell cmdlets.
Enabling PowerShell to connect to Azure using MSOL
On the 1E server where the Microsoft Office 365 connector will be executed, PowerShell needs to connect to Azure using MSOL, which requires the following two modules installed:
-
Install-Module -Name Microsoft.Graph
-
Install-Module -Name MsOnline
You may see one of the following warnings when installing a module:
-
WARNING: Unable to download from URI 'https://go.microsoft.com/fwlink/?LinkID=627338&clcid=0x409' to ''.
-
WARNING: Unable to download the list of available providers. Check your internet connection
If you see one of these warnings, run the following command first:
[Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12Preparing an AAD application
-
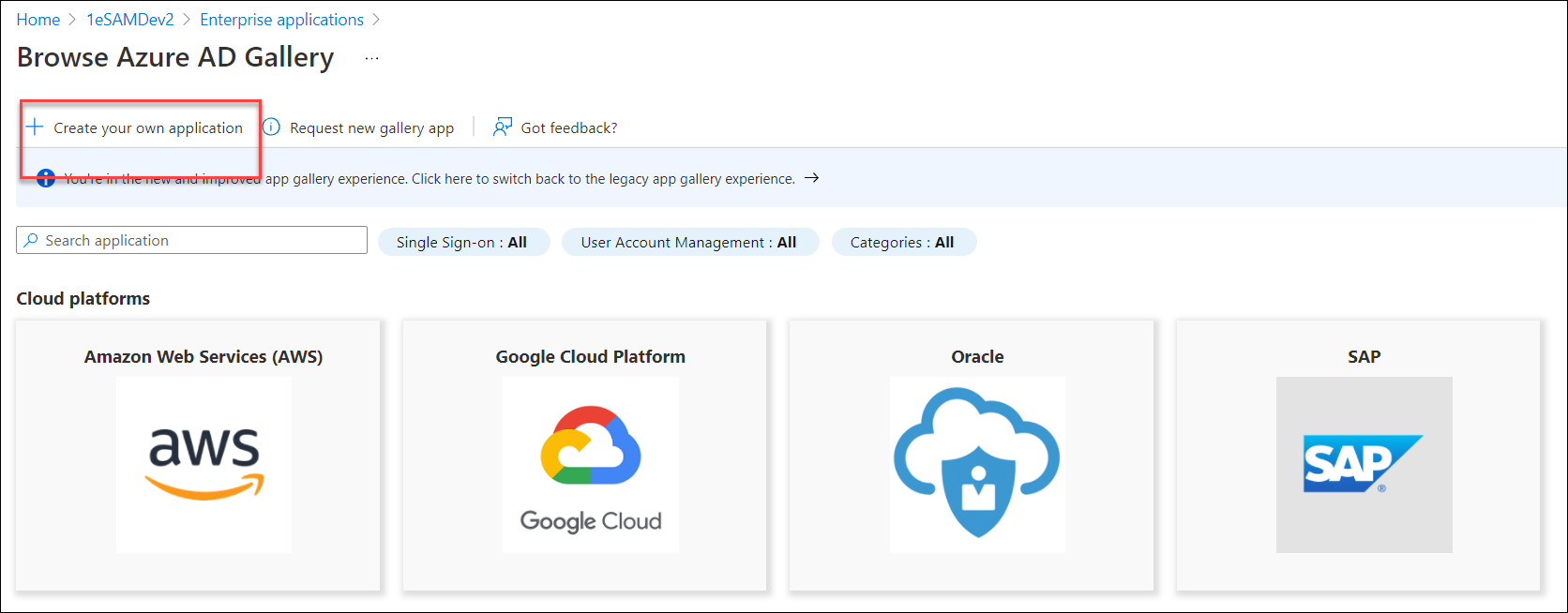
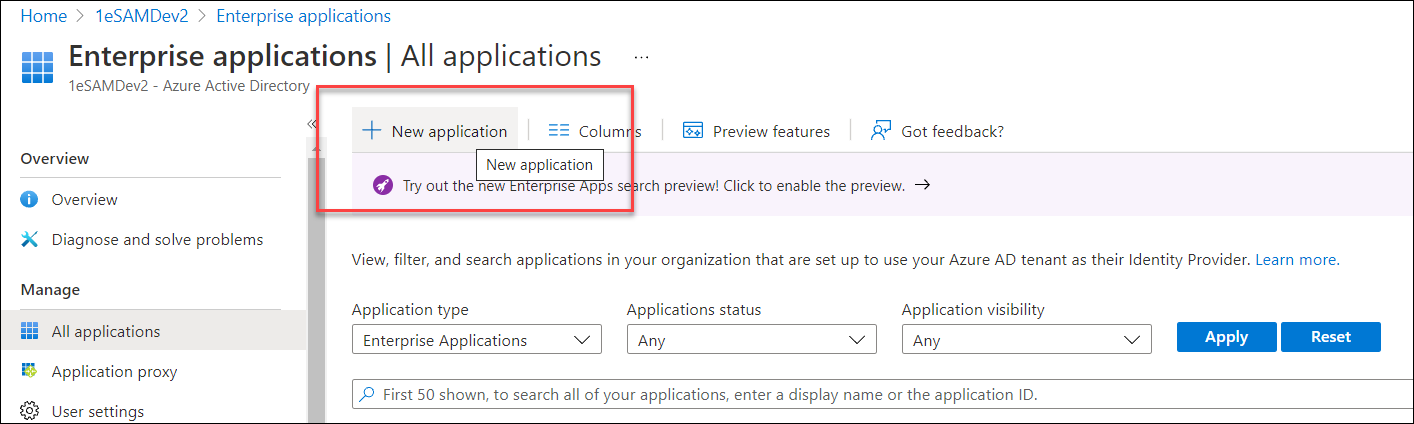
In your Microsoft Entra ID console, navigate to Enterprise applications and click New application.
-
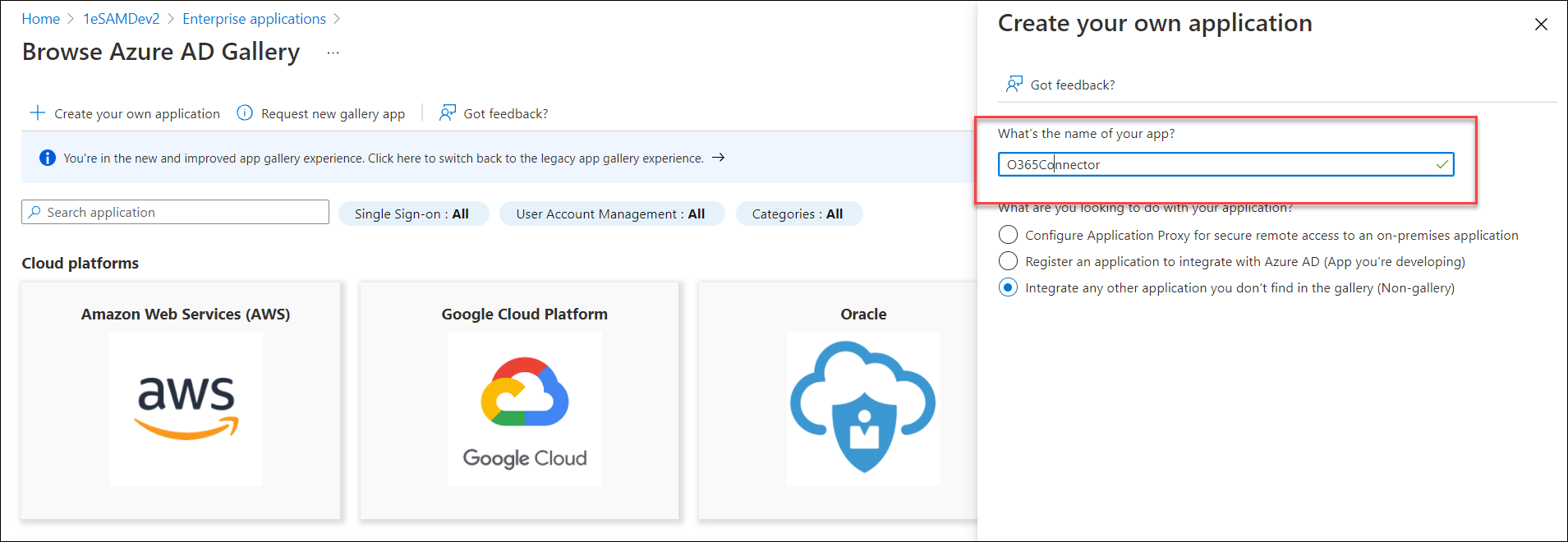
Create a non-gallery application.
-
Provide a name for the application, for example, 1E O365 Connector. In this example, we select the Integrate any other application you don't find in the gallery (Non-gallery) option.
-
Click Create in the bottom left of the screen.
-
In the Overview tab of the new application, copy the Application ID value as this will be required for the connector.
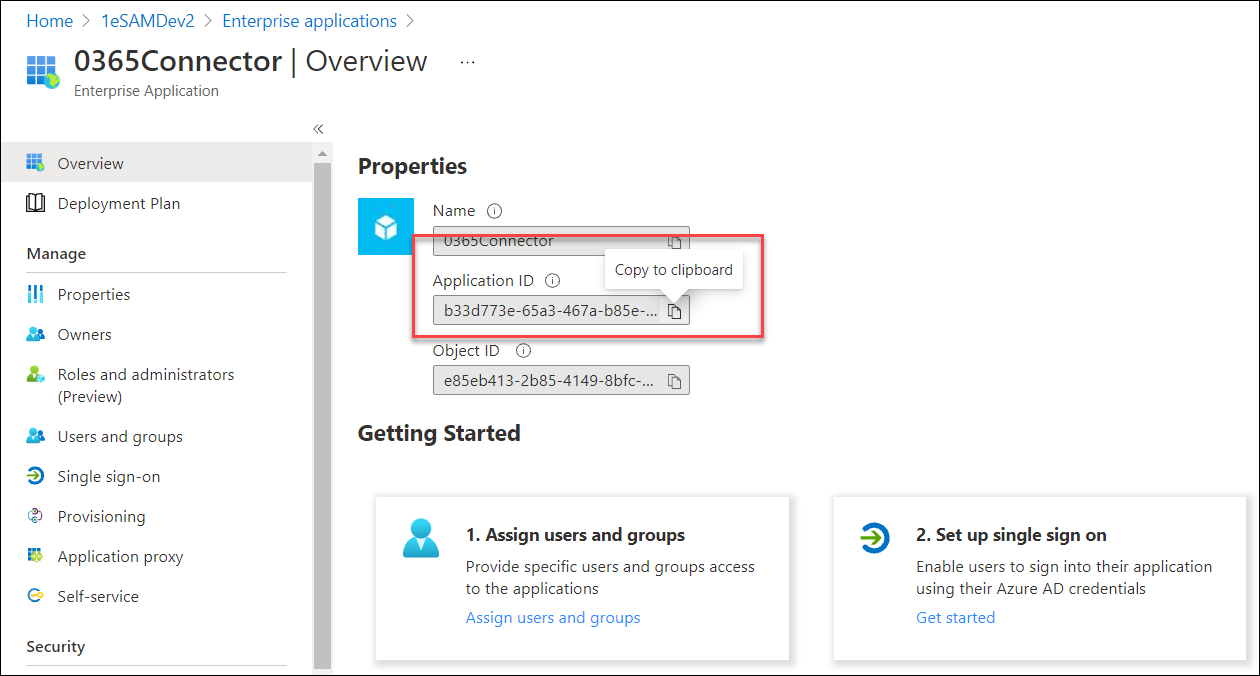
In 1E, the Application ID is called Tenant Id.
Adding app permissions
-
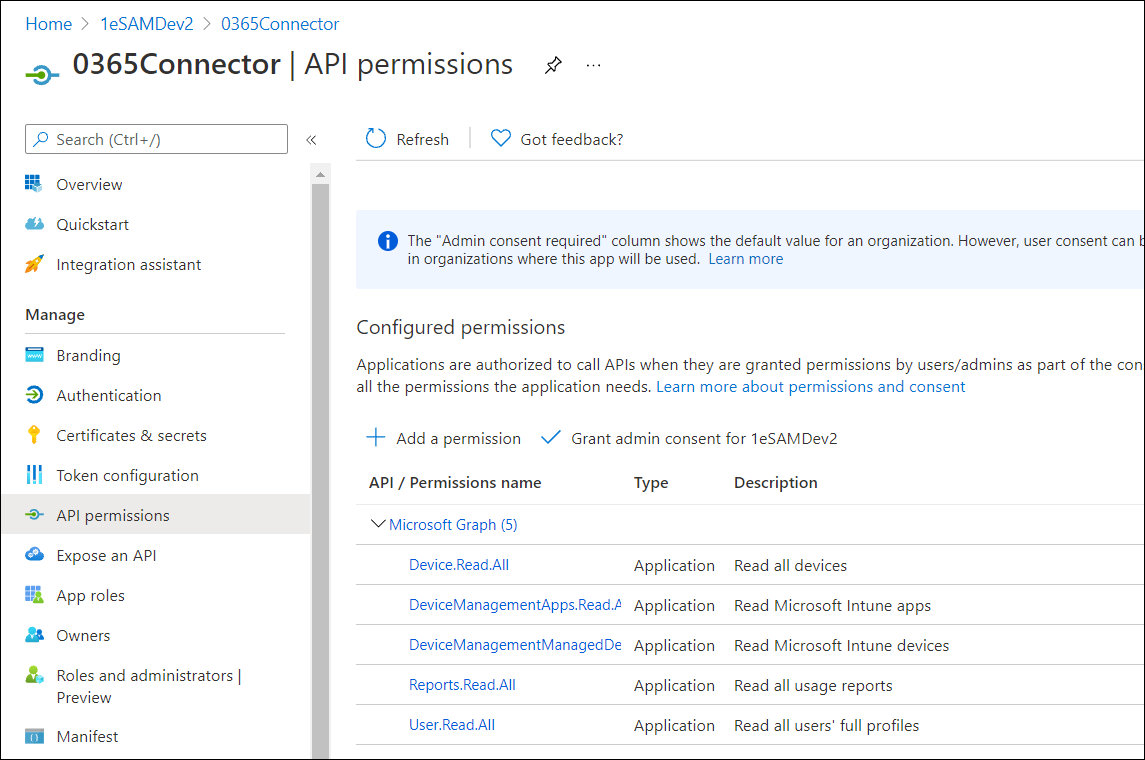
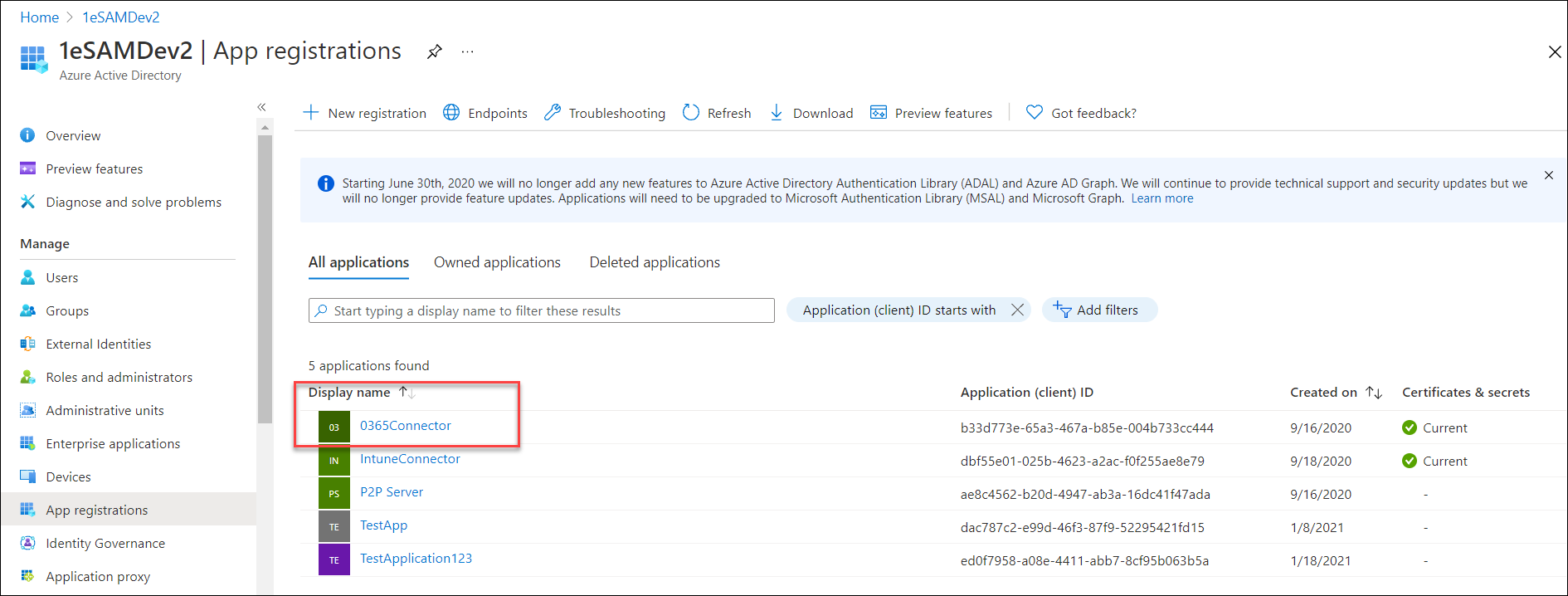
Click the App registrations node of AAD, and click the name of the new application under the All Applications tab.
-
In the Manage > API permissions node, click Add a permission.
-
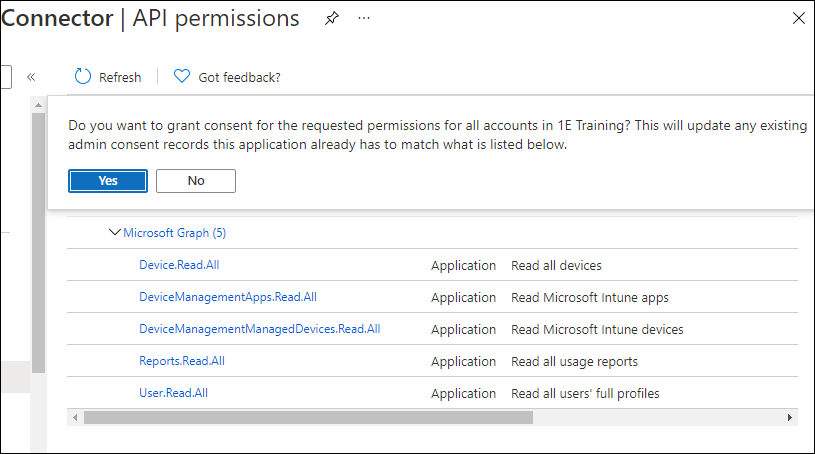
Click the Microsoft Graph tile, then click Application permissions.
-
Scroll through the list of API permissions, and select them as appropriate using the following guide, then click Add permissions.
Group
Permission
Device
Read.All
DeviceManagementApps
Read.All
DeviceManagementManagedDevices
Read.All
Reports
Read.All
User
Read.All
-
Click Grant admin consent for <organization>, where <organization> is the organization you set when you created your Intune instance. This means that as an administrator for your organization, you're consenting that the users of the application can use these permissions. Click Yes to confirm.
Adding a client secret
-
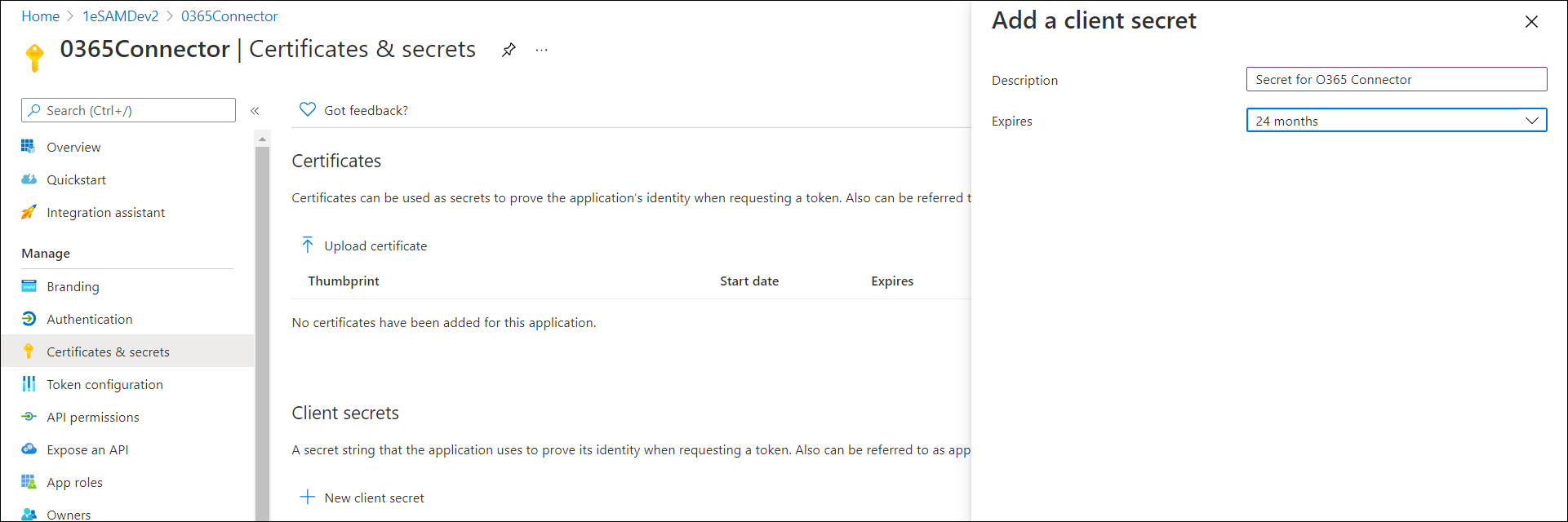
Click the Certificates & secrets node and then click New client secret.
-
In the Add a client secret form that opens, add a description, select an expiry, and then click Add.
-
Copy the new client secret value and save it, as you won't be able to retrieve it after you perform another operation or leave this page.
If you navigate away from the Certificates & secrets page and have not copied the secret value, you will have to delete the client secret and recreate it as you will be unable to copy it again.
Adding a user with the necessary permissions to run the PowerShell scripts
An AAD user with Reports reader permissions must be made available in your organization's blade. The credentials for this user will be set in the Microsoft Office 365 connector when it is created in 1E.
Adding the connector
-
Navigate to Settings > Configuration > Connectors.
-
Click Add.
-
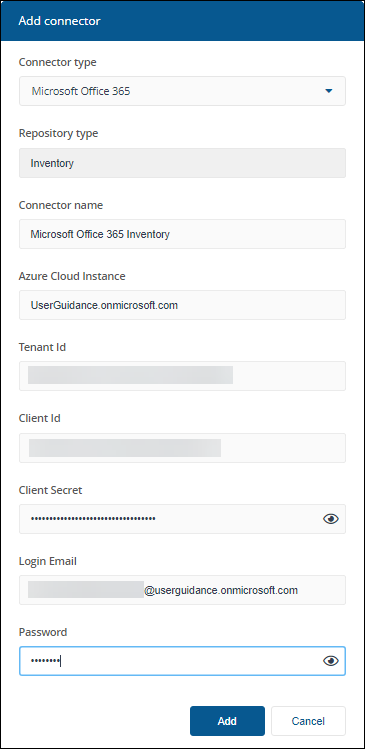
In the Add Connector pop-up window, select Microsoft Office 365 as the connector type.
-
In Connector name, enter a logical name for this connector.
Use a naming convention for connector names, for example, <connector type> <scope> <RCR>. Scope describes where data is coming from or what it's being used for, for example, Demo, Test, Lab, Q2 Audit. Include RCR in the name if the Run Consolidation Reports option is available and you have enabled it.
-
In Azure Cloud Instance, enter the URL for your Intune implementation. If you leave this field blank, AzurePublic is used as a default. For information on Azure Cloud Instance, refer to this Microsoft article.
-
In Tenant Id, enter your Azure tenant ID, available in the Overview node of your AAD console.
-
In Client Id, enter your registered application clientID.
-
In Client Secret, enter the specific client secret value that you created for your Enterprise Application. Refer to Adding a client secret.
-
In Login Email, enter the email address of the user with the appropriate permissions.
-
In Password, enter the password associated with the login email.
-
For information on how to test or delete a connector, and how to sync data into a repository, refer to Connectors page.